Maia Estianty just wanted to order some food online. Instead, her e-wallet was depleted.
In December 2019, Estianty ordered a meal from Gojek’s food delivery arm, GoFood. It wasn’t long before the driver who was supposed to transport her order called to say his motorcycle broke down. Fortunately, he said, his colleague could fulfill the order. All Estianty needed to do was dial a number sent by the driver to confirm the order transfer process.
Estianty did as the driver said. She didn’t realize that the string was actually a code for call forwarding, which gave the driver access to her phone. He hijacked her Gojek account and depleted nearly IDR 800,000, or USD 57, of her GoPay credit, then attempted to access other apps on her phone. Quickly, Estianty canceled her credit cards and deactivated her phone number.
Her experience was shared in a now-deleted Instagram post and attracted public attention. Gojek reimbursed Estianty for her lost credit and condemned the “social engineering” perpetuated by scammers through their service, according to local media outlet Kompas.
Unfortunately, not all victims are as lucky as Estianty. Similar scams are rampant in Indonesia, and few victims ever see media coverage or compensation.
Catching up with evolving strategies for fraud
Indonesia has 197 million internet users—and a digital literacy deficiency, especially regarding personal digital security. Most users, even young people who are often presumed to be more aware of their online footprint, are susceptible to fraud, according to a report published by the Center for Digital Society (CfDS), a digital research center at Gajah Mada University.
Among the methods for online fraud, social engineering is by far the most common. It is a process where perpetrators abuse a victim’s trust. This form of scamming poses a high risk in Indonesia because of a lack of awareness, according to the CfDS’ report. Victims are tricked into sharing sensitive information, like one-time passwords (OTP), under false pretenses such as “you’ve won the lottery” or “this is a system requirement.” This gives scammers control of their victim’s account, like in Estianty’s case. CfDS’s report indicates that social engineering techniques have become more advanced.
While high-resolution portraits and realistic masks have been used to bypass facial recognition locks, biometric identification makes fraud more difficult by folding a user’s physical traits into the identity confirmation process. If anomalous behavior is detected in an e-wallet account, for instance, the platform could demand facial or fingerprint identification before processing an atypical transaction—or freeze the account if verification fails.
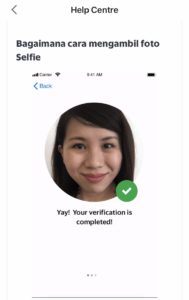
Tech companies in Indonesia are now looking into biometric identification to shore up security for users. This year, Grab rolled out fingerprint identification as an alternative to alphanumeric passwords and began to require selfie authentication for drivers and users.
“Through the years, we’ve realized that fraudsters never stop. What they do is stop the current way of tricking users to evolve and come up with other tricks,” said Wui Ngiap Foo, Grab’s head of technology, integrity group, transport, and patents office, to KrASIA. “To keep up, we have to evolve as well.”
Biometric identification serves as a second layer of protection in Grab’s security system, GrabDefense. The company also uses artificial intelligence (AI) for behavioral analysis within user accounts. Foo said that the AI distinguishes genuine users from fraudulent ones based on a range of user characteristics and data signals, such as browsing time and transaction amounts.
For example, hijacked accounts tend to log less time on the app but attempt to initiate transfers that carry unusually high amounts. When this is flagged, the system will prompt for additional authentication, like submitting a selfie, before the transactions are approved. “When the models are confident that fraud has taken place, there is typically an immediate ban or suspension,” Foo said.
In July, Gojek’s face recognition feature went online as a means to prevent fraudulent transactions on the app. Indonesian e-wallet platform Dana did the same for its login process. Dana CEO and co-founder Vince Iswara said that more users are activating the feature as it’s proven to be effective in preventing account hijackings. “Due to its success, we are currently expanding the features not only for logins, but also in other cases,” he said.
All of the companies KrASIA approached said they do not share the biometric data that they collect. “Grab takes personal data protection very seriously. Passenger selfies are securely stored and not shared with anyone, including the drivers,” Foo said.
Gojek’s privacy policy states that the company does not save users’ biometric data on their own system. Instead, the data is stored locally on users’ devices.
Lingering blind spots
Right now, fingerprints and retinal data are the only biometric traits referenced in Indonesian legislation, specifically in the country’s population administration law, said Wahyudi Djafar, deputy director of the Institute for Policy Research and Advocacy (ELSAM). “We can say that biometric data is still not strictly regulated in Indonesia for now,” he told KrASIA.
An updated version of biometric data classification, which covers facial features, is included in the personal data protection bill drafted in January 2020. However, it has not been passed into law by the Indonesian parliament. According to the draft, biometric data is “specific personal data” that can only be processed for limited purposes, such as in criminal cases or emergency health crises.
A security expert from antivirus and cybersecurity firm Vaksincom, Alfons Tanujaya, said that biometric identification helps prevent fraud. “It is different from OTP, which is in the form of digital numbers that can be seen or shared through texts. Biometrics cannot be copied because they require a physical presence,” he told KrASIA.
However, Teguh Aprianto, the founder of Ethical Hacker Indonesia, noticed a loophole. Logins that utilize biometric data do not completely replace password logins; they are only optional features. Since the data is stored on the user’s device, he said, it doesn’t protect them from hacking attempts using a different device, such as Estianty’s case. “The fingerprint login will be useless and the fraudster can still hijack the account using OTP if he could access the account owner’s phone.”
Aprianto said digital platforms should send an in-app notification, not an SMS, if an unknown device is attempting to log in. “The new device should only be able to log in after there’s an approval from the primary device,” Aprianto said.
Startups must remain vigilant to counter fraud that uses social engineering, since there are still vulnerabilities for fraudsters to exploit.


